The damage done by the leaking of the UK Ambassador’s correspondence, about the President of the United States, is a timely reminder that there are always risks in communicating in a digital world.

The FCO will have ‘state of the art’ IT security systems in place and aligned procedures that ensure sensitive information is handled with the appropriate security classification caveats. However, alongside this, ambassadors are encouraged to ‘say it how it is’ and to speak truth to power. This frank and honest approach allows the UK Government to assess situations and then make its mind up about decisions and policy. The problem with this approach is that fails to take into consideration the new risks that digital communications have brought to governments. Once an ambassador clicks ‘send’, he or she must trust that the system will protect the information and that relies on both the technology employed and trust in the very people that have access to it. Given that very similar leaks (on a much larger scale) happened to the US Government over the Wikileaks scandal, one would have thought that this incident alone would have been enough to change the way UK Ambassadors report back to London, especially in high profile embassies. It is clear that this has not happened.
Lessons Learned
- There is no such things as a totally secure communication system
- However secure communications are, the moment they’re read by someone they become vulnerable to their intentions – which may well be at odds with the author’s intentions.
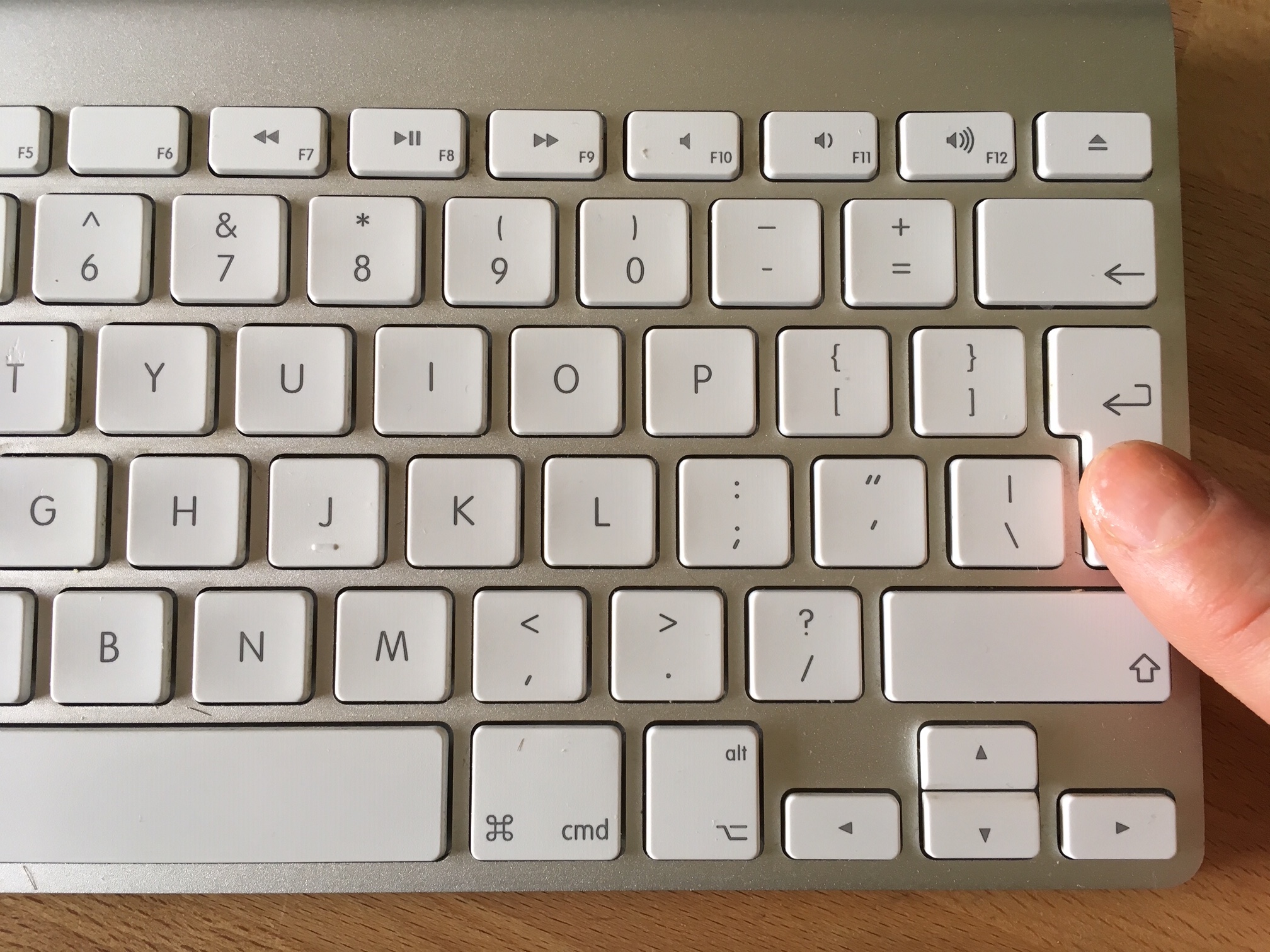
- The minute the author presses the Return Button, or clicks ‘send’, they immediately lose control of where that data may end up and how it may be used.
You don’t need to be an ambassador to fall victim to a communications leak. The risks of communicating in the digital era threatens all organisations – so, before circulating confidential, classified or even sensitive information, employees should ask themselves the following questions:
- How sensitive is the information I’m about to send?
- Does it need to be sent at all?
- Is it written in a way that will be understood and not cause offence?
- Is this the right means in which to send such information?
- Who will have access to this information and what can be done to restrict its wider distribution?
- What might be the consequences of this information being more widely circulated?
- What can be done to ensure that any leak is traceable?

by Associate Director – Harry Fullerton






